The CBC Cyber Range
OnNet and Cyber ranges developed a storyline that has a unique set of infrastructures that showcase how a terror network develops capability online, to plan and fund operations before executing a terror action. This exercise takes you deep into development of Course of Action and other CNO documentations before actions on. This range and its class would extremely benefit Intelligence services and Military cyber operators. It also trains the beginner-operator how you present to a commander the assessment, understanding of the Operational Environment, targeting/analyzing Center of Gravity and the game plan to execute an effective offensive cyber operation, with maximum success. Students are trained and introduced to beginner classes on Windows API and further into Data Structures like Process Environment Block, Windows Loader Structure, Thread Environment Block etc. From there, students are shown how to build tools from scratch that can be deployed with evasion to take screenshots, hook keyboard for logging, enumerate tokens, exfiltrating of data covertly, build custom stagers, develop loaders, understand NTAPI, Play with Syscalls, Evade Sysmon/EDRs, Shellcoding, Evade AMSI and other technicalities used on the battleground during OCOs. Students are then trained how to build operations infrastructure, from Dead Drop servers, Watering Hole sites, phishing boxes, develop legends, staging servers, to Covert Listening Posts and Team servers for intelligence analysis, storage and dissemination.
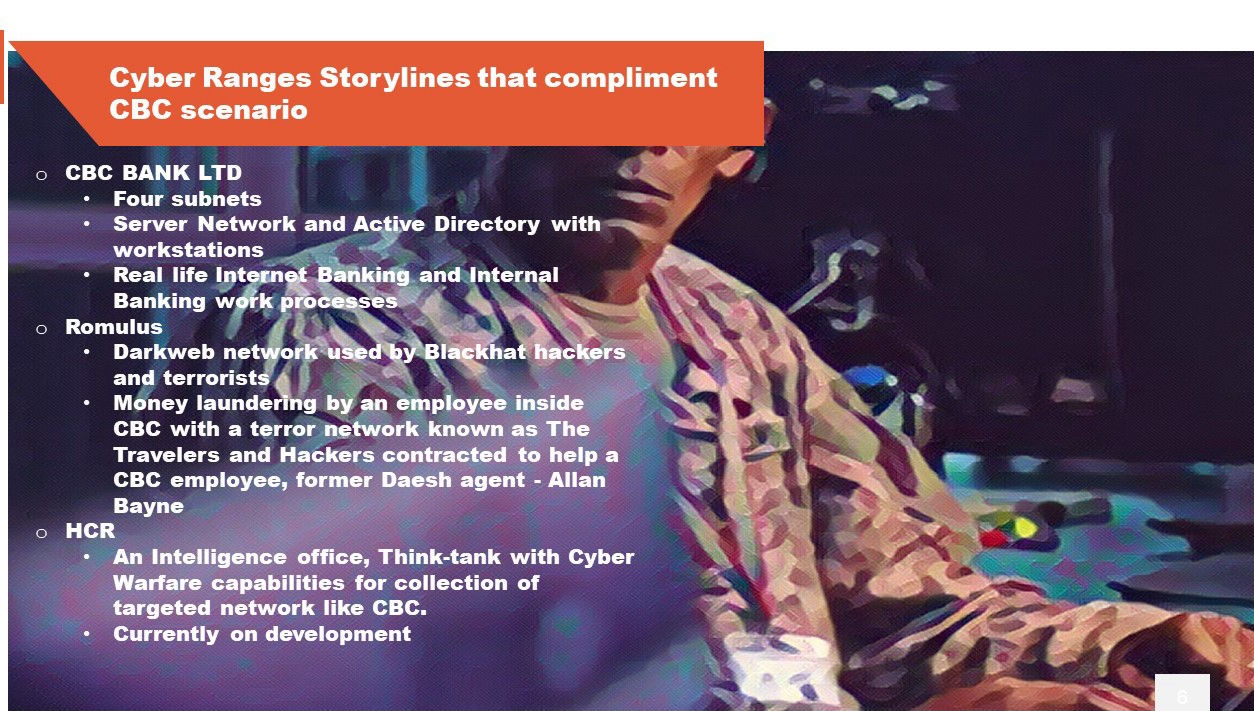
This range is one of a kind where you have to find the terror insider, who/how, he/she; is cleaning money inside the bank, who is their accomplice, how he communicates with his handlers and uncover the next 911 style attack and which city is getting hit and how to stop them from accomplishing their objectives.
To find more about Cyber Ranges:
Click below and have your mind blown away with the resources for training, learning and upping your cyber resilience posture.
Go learn and use several upcoming realistic Scenarios.
Posted by the Chuksjonia, CEO OnNet Group on 15th October 2021